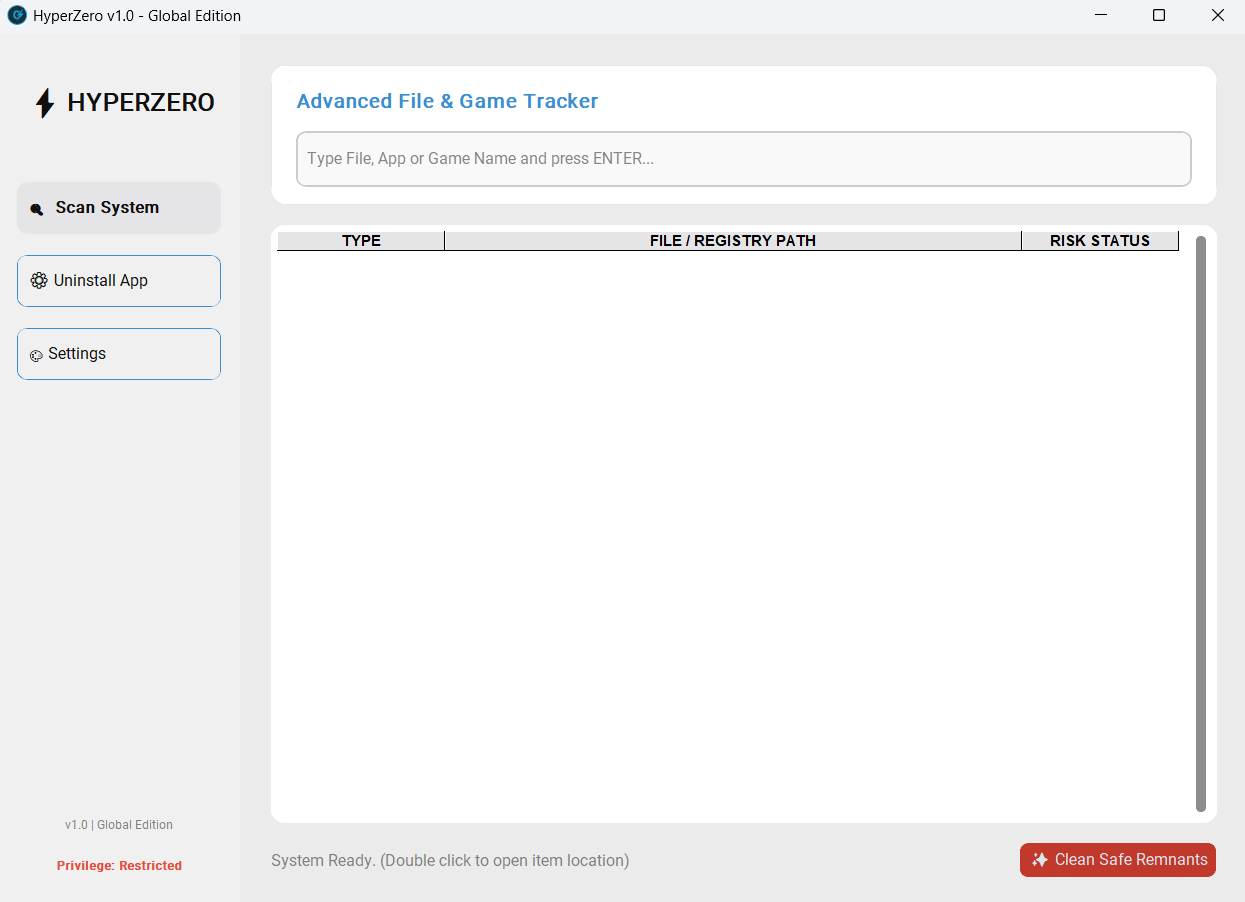
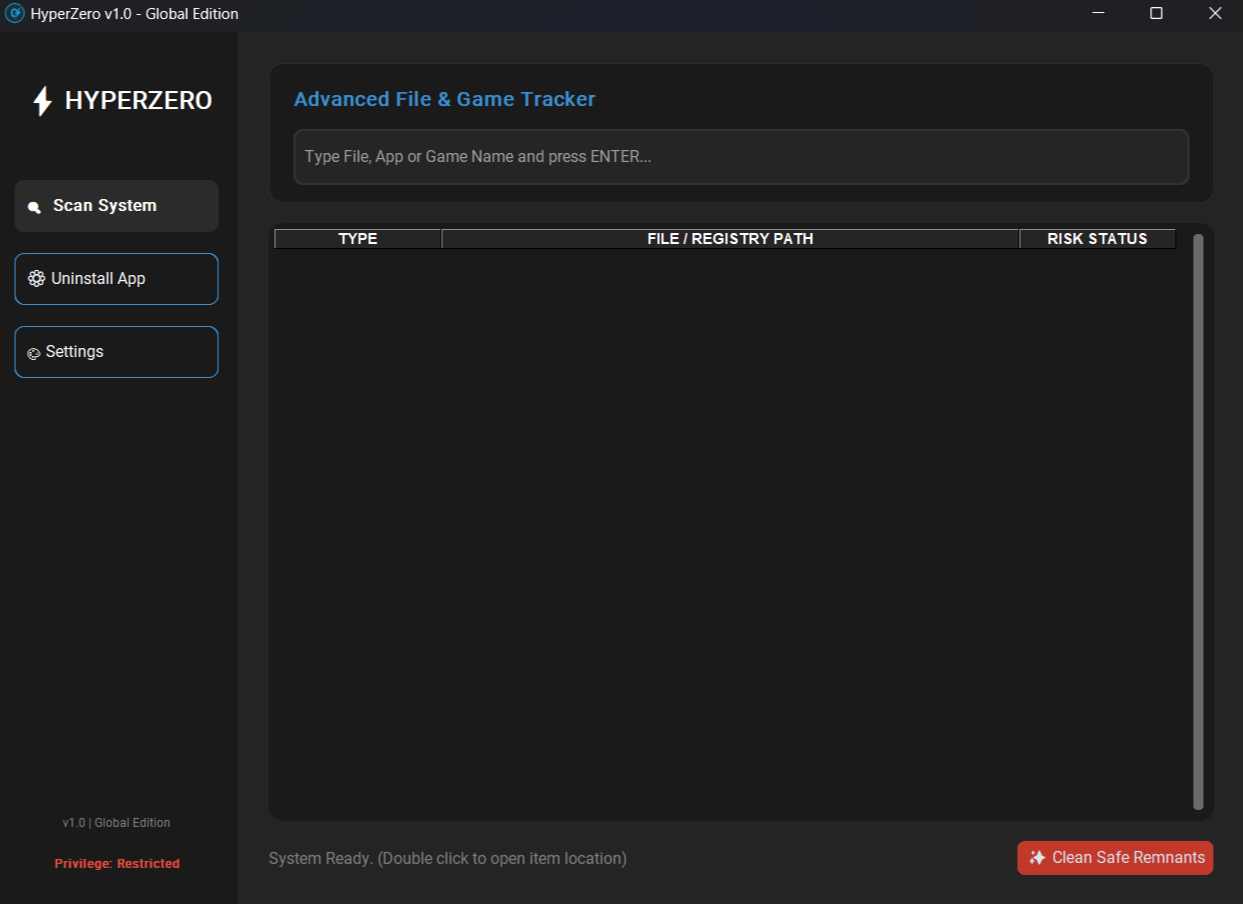
Sildiğiniz programdan geriye ne kaldıysa, saniyeler içinde bulun ve güvenle temizleyin. Find what an uninstaller leaves behind in seconds — and clean it up safely.
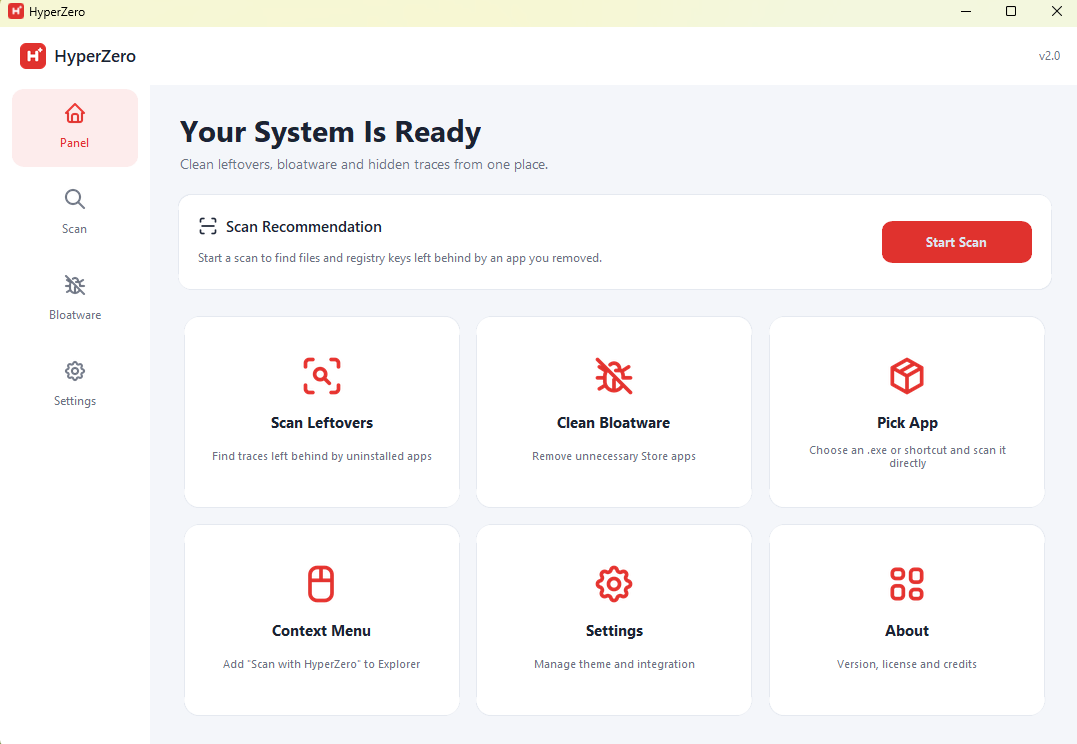
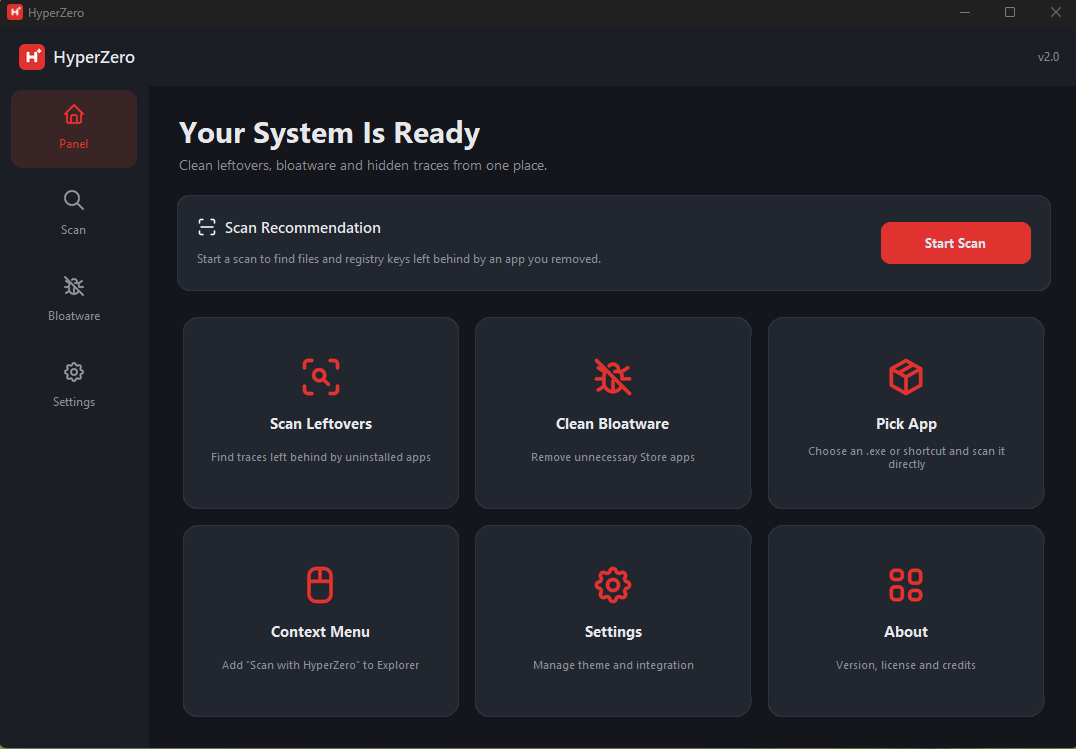
HyperZero v2, dosya sisteminin ana dizinini doğrudan okuyarak tüm diskinizi saniyeler içinde tarar. Kalıntıları Güvenli / Orta / Kritik diye puanlar, bloatware'i kaldırır — ve dosya/registry silmelerini yedekleyip tek tıkla geri almanıza izin verir.
HyperZero v2 reads the file system's master index directly to scan your whole disk in seconds. It scores remnants as Safe / Medium / Critical, removes bloatware — and backs up file/registry deletions so you can undo them in one click.